When confidence outpaces control: lessons from the MFS collapse
19th May 2026
Katherine Odendaal and Noemi Klein
Three Aston Martins, two Mercedes, six Ferraris and three Rolls-Royces. Just some of the benefits Paresh Raja is alleged to have received as part of what the administrators of Market Financial Solutions (MFS) describe as the “systematic plundering” of £1.3bn, as set out in a High Court claim on 5 May 2026.
The collapse of MFS is not simply another specialist lender failure. It represents a more uncomfortable type of event: one that sits at the intersection of fraud, anti-money laundering (AML), third party assurance, and indirect risk exposure.[1]
The issue is not only the scale of losses that have emerged. It is that these losses appear to have crystallised through structures perceived as one step removed from primary credit risk, including sponsor-linked exposures, warehousing arrangements, securitisation channels and collateral reporting frameworks that counterparties may have assumed were already understood or adequately reviewed.[2]
Market Impact
The market reaction has made this difficult to ignore. On 5 May 2026, HSBC disclosed a $400 million fraud-related charge linked to what it described as a “secondary securitisation exposure with a financial sponsor in the UK”, with reporting identifying the underlying exposure as connected to MFS.[3] Barclays had previously disclosed a £228 million impairment linked to the same collapse.[4]
What began as the failure of a Mayfair-based specialist lender has moved beyond a niche insolvency story and into the balance sheets, risk committees and control assessments of major financial institutions. Reporting around the MFS collapse has identified a wider circle of banks and private credit participants with exposure to MFS, or connected structures, reinforcing that the issue extends beyond impairments already recognised.[5]
Regulatory Clarity
That matters because MFS was not a mainstream bank operating within the full Financial Conduct Authority (FCA) perimeter. The FCA has stated that MFS was an Annex 1 firm, meaning it was registered with, and supervised, by the regulator solely for compliance with the Money Laundering Regulations and was not subject to wider FCA scrutiny.[6]
MFS entered administration on 25 February 2026. The FCA opened an enforcement investigation on 20 March 2026.
One of the most important facts in this case is that the scope of FCA supervision was narrower than what many counterparties would assume when they hear that a firm is “FCA supervised”. The distinction also raises further questions about enforcement reach. While Annex 1 firms sit outside the FCA’s full authorisation perimeter, they remain subject to the Money Laundering Regulations and can therefore still face significant supervisory and enforcement action in that context. The practical issue is not whether enforcement exists, but whether market participants fully appreciate the difference in supervisory scrutiny and scope when forming their risk assumptions.
That distinction should not be treated as a technicality. It goes directly to the degree of comfort that banks, sponsors, and counterparties can take from external status labels. An Annex 1 registration is not the same thing as prudential supervision, broader conduct supervision, or a regulatory judgement on the overall soundness of a business model. If institutions treat those categories as interchangeable, they risk importing a false sense of assurance into underwriting, onboarding, and monitoring decisions.
This is not only a fraud story
It is tempting to frame MFS as a straightforward fraud event and stop there. That would be too narrow.
Allegations reported around the collapse include potential double pledging of collateral, irregularities in key bank accounts, and significant shortfalls between amounts advanced and collateral apparently available.[7] Whether those allegations are ultimately proven is a matter for the legal process. The more pertinent question from a controls perspective is: what kind of risk management framework allowed risk to travel so far before loss crystallised?
This is precisely why policymakers have been growing more uneasy about private credit and adjacent non-bank lending structures. The Bank of England has launched a system-wide exploratory scenario exercise focused on private markets, noting that private credit and private equity now play a significant role in financing UK companies and real estate.[8] The Financial Stability Board has likewise published a report on vulnerabilities in private credit, highlighting opacity, valuation uncertainty, and deepening ties with banks and insurers.[9]
MFS is therefore not an isolated event. It has emerged in a market already under scrutiny for precisely these structural reasons.
Indirect Risk Transmission
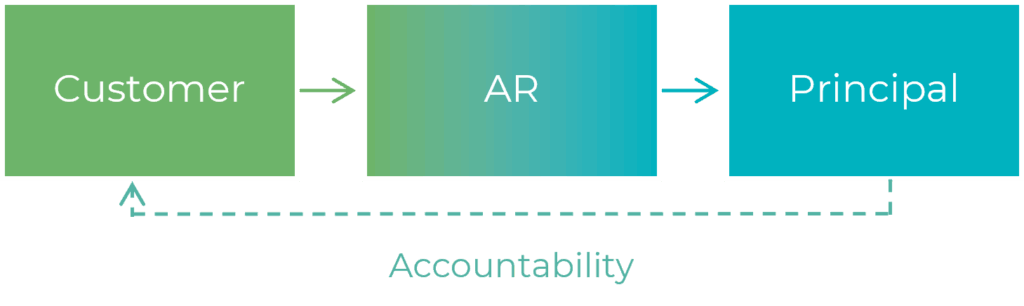
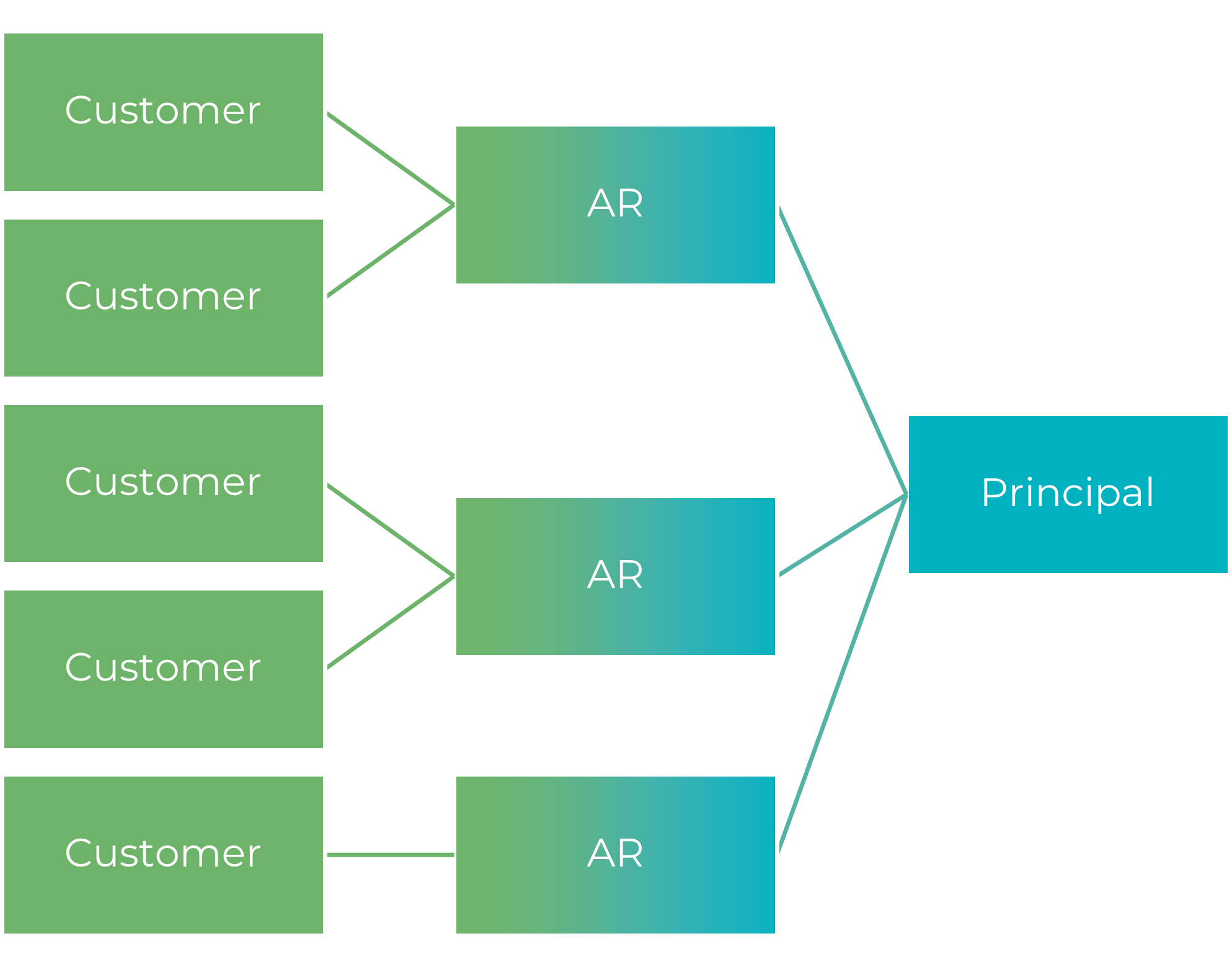
The impairments recognised by banks matter not only because the numbers are large, but because they show how loss transmission can occur indirectly, through sponsors, securitisations, warehouses, and funding structures that can feel one-step removed from the originating risk.
In practice, this means banks should be wary of thinking fraud risk purely resides at the point of origination. In layered structures, the relevant question is whether firms truly understand the control environment around the originator, the integrity of collateral reporting, the independence of servicing flows, and the governance quality of the wider ecosystem through which exposure is carried.
Why the AML angle matters more than it may first appear
The AML dimension is not peripheral to this story. It is central.
The FCA has been explicit that some Annex 1 firms are still not getting the basics right, and has identified recurring weaknesses, including discrepancies between registered and actual activities, financial crime controls that did not keep pace with growth, poor risk assessments, and inadequate resourcing and oversight.
These findings predate the MFS collapse. They were communicated by the FCA more broadly as part of its supervisory work on Annex 1 firms.[10] The MFS enforcement investigation therefore lands against a backdrop in which the regulator had already warned that this part of the market contains firms with weak AML foundations.
That point should resonate particularly strongly with institutions exposed to real estate backed lending, high-velocity growth, cross-border ownership structures, and higher-risk source of wealth characteristics. In those environments, managing financial crime risk cannot be reduced to onboarding documentation and sanctions screening alone. It has to operate as part of a broader challenge framework. It requires exercising contractual audit rights including:
- understanding beneficial ownership.
- testing source of funds plausibility.
- identifying unusual collateral patterns.
- validating the commercial rationale of transactions.
- escalating where business growth begins to outpace the control infrastructure intended to govern it.
When the FCA says some Annex 1 firms have not kept pace with business growth, it is really pointing to a deeper truth: scale can amplify weaknesses faster than governance notices them.
What about the external auditor and other lines of assurance?
This is where the case becomes especially uncomfortable.
MFS filed accounts up to 31 December 2024 before entering administration in February 2026.[11] This is not an indicator of audit failure, nor should statutory audit be expected to function as a generic anti-fraud or AML examination.
However, audit has a defined scope. So do regulatory reviews. But when a business presents recent accounts that has passed through external assurance processes, and yet shortly afterwards becomes the subject of administration, alleged fraud claims and an FCA enforcement investigation, boards and lenders are entitled to ask a hard question: did assurance provide clarity, or did it merely provide comfort?[12]
That is not a rhetorical distinction. Comfort-led assurance tends to focus on whether a control exists, whether a process is documented, and whether management can evidence a framework. Challenge-led assurance asks tougher questions:
- Is the data feeding that framework reliable?
- Are exceptions truly escalated?
- Can management information be independently reconciled?
- Is management information sufficiently timely to inform forward looking decisions rather than only understand outcomes retrospectively?
- Are growth assumptions credible?
- Does the review scope reflect the actual risk profile rather than the nominal perimeter?
In fast-moving or less transparent environments, that difference becomes decisive.
The public commentary around MFS has also sharpened scrutiny on third-party AML reviews. The Financial Times reported that MFS was given an all clear in a 2024 FCA review, where the relevant law firm reported to the regulator that MFS was complying with the relevant AML rules. That does not, by itself, invalidate the review or establish fault. It does, however, raise a broader question about how regulator mandated reviews are scoped, how much reliance institutions place on them, and whether they are treated as substitutes for ongoing independent judgement across the first, second, and third lines of defence within the firm.
The FCA’s own explanation of the skilled person regime underlines that such reviews are tools to inform supervision, not guarantees of future soundness.[13]
Practical implications for banks
For banks and funders, the MFS collapse should prompt a retest of how indirect fraud and AML exposure is triangulated, identified, and challenged. That means asking whether the evaluation of risk, and the associated risk management frameworks, are sufficiently robust not only for direct borrowers, but also for sponsors, originators, servicers, connected entities and underlying collateral. It means testing whether legal rights over collateral are genuinely exclusive and enforceable, whether cash collections can be independently traced, whether concentrations are visible across structures, and whether warning signs in one part of the relationship are allowed to inform risk appetite definitions and decisions elsewhere.
Where structures are sufficiently layered, institutions can appear diversified while in reality, they are accumulating exposure to the same control weakness through different channels.
Fraud Risk Evolution
For fraud prevention teams, the implication is equally important. The next generation of loss events is unlikely to sit neatly inside a single ‘fraud’ category. More often, the indicators will be distributed across credit, financial crime, legal, audit, operations, servicing, governance, and data quality.
The institutions that respond best will be those that can connect those signals early, challenge apparent control comfort, and investigate quickly before the issue requires a write-down, triggers regulatory investigation, or leads to fines, penalties, and costly remediation.
The strategic opportunity is not simply to catalogue more red flags or isolated anomalies. It is to surface a common pattern that reveals a deeper structural weakness. Furthermore, the objective is not only early identification, but timely remediation before issues begin to impair a firm’s ability to operate effectively, sustain profitability, or withstand regulatory scrutiny.
[1] Investigation into Market Financial Solutions Limited | FCA
[2] UK Regulator Opens Probe Into Market Financial Solutions After Insolvency – Bloomberg
[3] HSBC Shares Slump 6% on Surprise $400 Million Hit Linked to MFS Collapse
[4] Barclays Eyes Over 50% Recovery on Collapsed UK Firm MFS as Asset Hunt Uncertain – Bloomberg
[5] Wall Street hit by UK mortgage lender collapse, raising fears of more credit ‘cockroaches’ | Reuters
[6] Investigation into Market Financial Solutions Limited | FCA
[7] MFS’s Collapse Refuels Double-Pledging Concerns Within the Private Credit Industry – Manatt, Phelps & Phillips, LLP
[8] Bank of England launches system-wide exploratory scenario exercise focused on private markets | Bank of England
[9] Report on Vulnerabilities in Private Credit
[10] FCA warns firms over anti-money laundering failings | FCA
[11] MARKET FINANCIAL SOLUTIONS LIMITED filing history – Find and update company information – GOV.UK
[12] DWF LLP | Financial Times
[13]Skilled person reviews | FCA
How HKA can help
For boards, lenders, sponsors and general counsel, the immediate priority is not to produce another generic ‘lessons learned’ list. It is to test where apparent assurance may be masking unexamined exposure. HKA supports clients by:
- investigating complex fraud concerns
- examining control breakdowns across all lines of defence
- testing whether governance, AML frameworks and underwriting align with actual risk.
In practice, that may mean conducting targeted fraud risk reviews across warehouse and securitisation exposures, assessing whether anti-financial crime controls in higher-risk lending ecosystems are proportionate to the business actually being written.
It may also mean investigating how warning signals moved, or failed to move, through committees, reporting lines, and assurance functions, or supporting institutions that need a defensible remediation plan after loss, regulatory scrutiny, or adverse press.
The key question after MFS is not whether this exact pattern will repeat, but it is where else institutions may still be relying on labels, comfort or inherited assumptions when the underlying risk picture is changing faster than their control framework, management information or assurance model can keep pace. That is often the point at which an advisory conversation becomes most useful, well before a concern matures into an enforcement case, an impairment, or a public challenge about what should have been seen sooner.